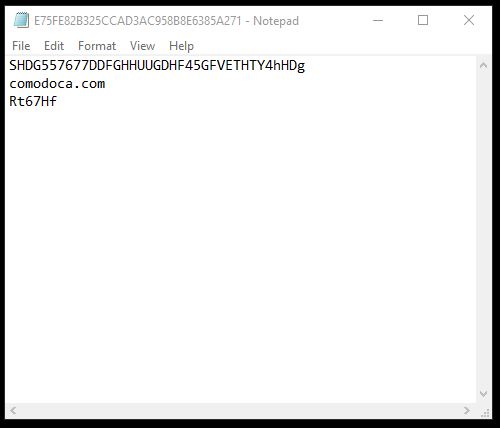
-connection-type-for-real-time-java-based-apis/2018_Nipat_Keystore_07-1.png)
Building a keystore file to be used with an HTTPS (or ENCRYPTED) connection type for real-time Java-based APIs | Devportal

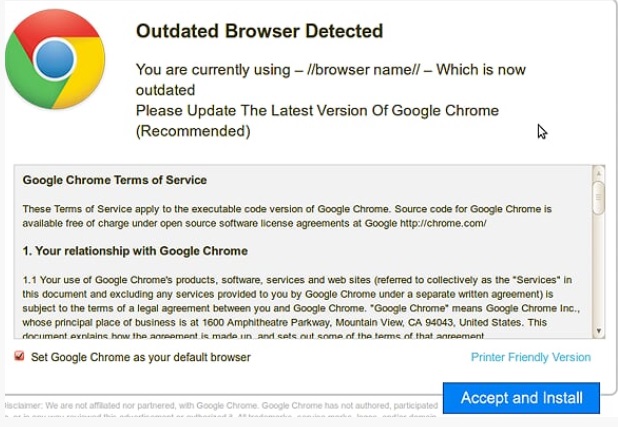
Sectigo has announced that it will transition from Comodo CA roots to USERTrust CA roots | LeaderSSL
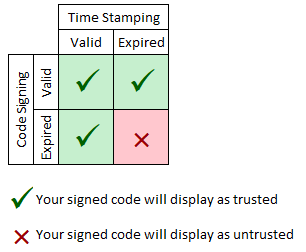
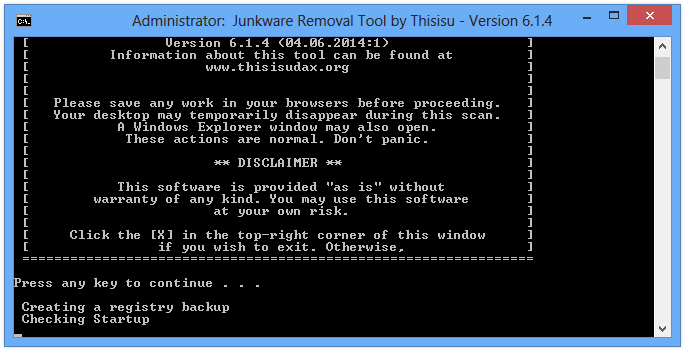
Sectigo (formerly Comodo) Time Stamping Service Expiration – What to Know and What to Do - Knowledge Base

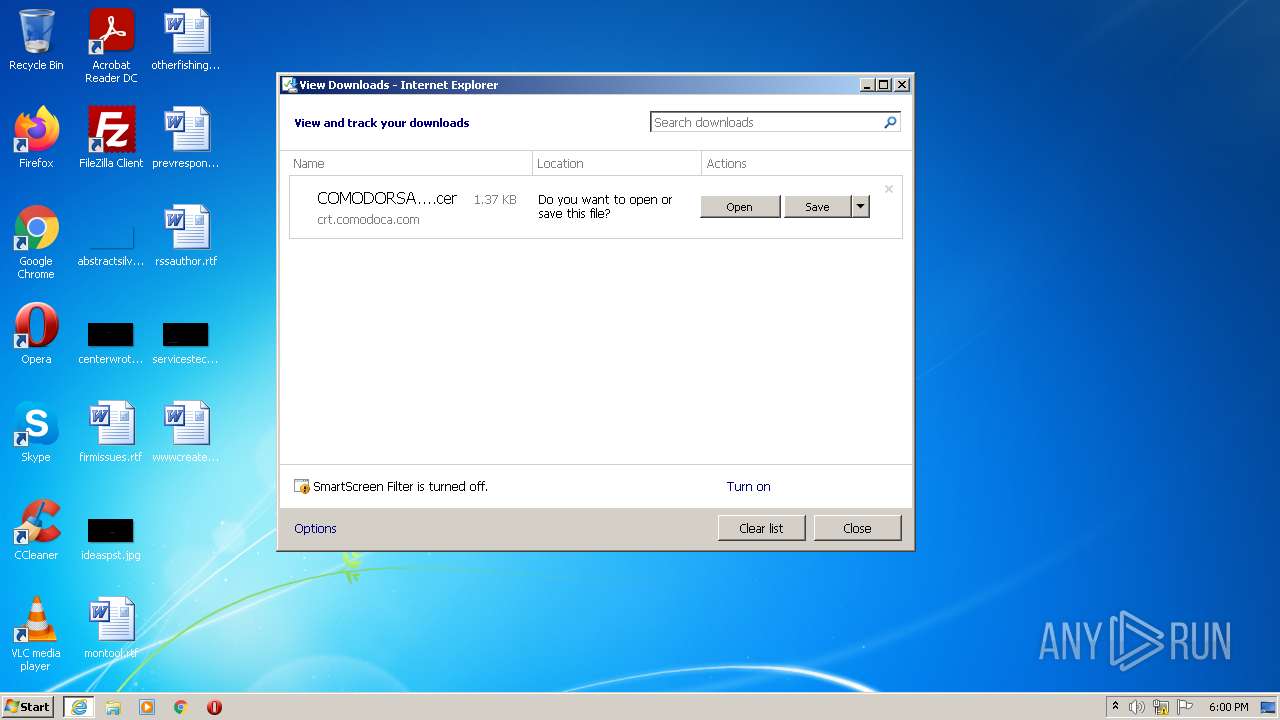
Malware analysis http://crl.comodoca.com/COMODORSACertificationAuthority.crl No threats detected | ANY.RUN - Malware Sandbox Online